MAX Intelligence: Low-Cost Disruption Tactics Reshape Global Supply Chain Risk
- MAX Security
Table of Contents

Low-cost sabotage and UAV interference are driving extreme uncertainty across global supply chains as asymmetric tactics exploit safety protocols to create persistent operational risks and structural financial pressures for infrastructure networks worldwide.
Executive Summary
-
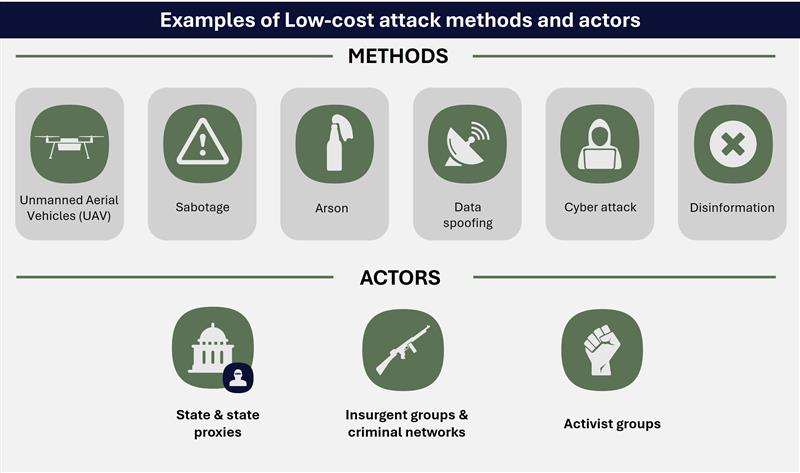
Low-cost and effort attack tactics including unmanned systems, sabotage, arson hoax alerts, and digital data distortions are increasingly being used by states, proxies, criminals, and activists to disrupt global infrastructure systems. These attacks are intended to cause disproportionate operational and economic consequences.
-
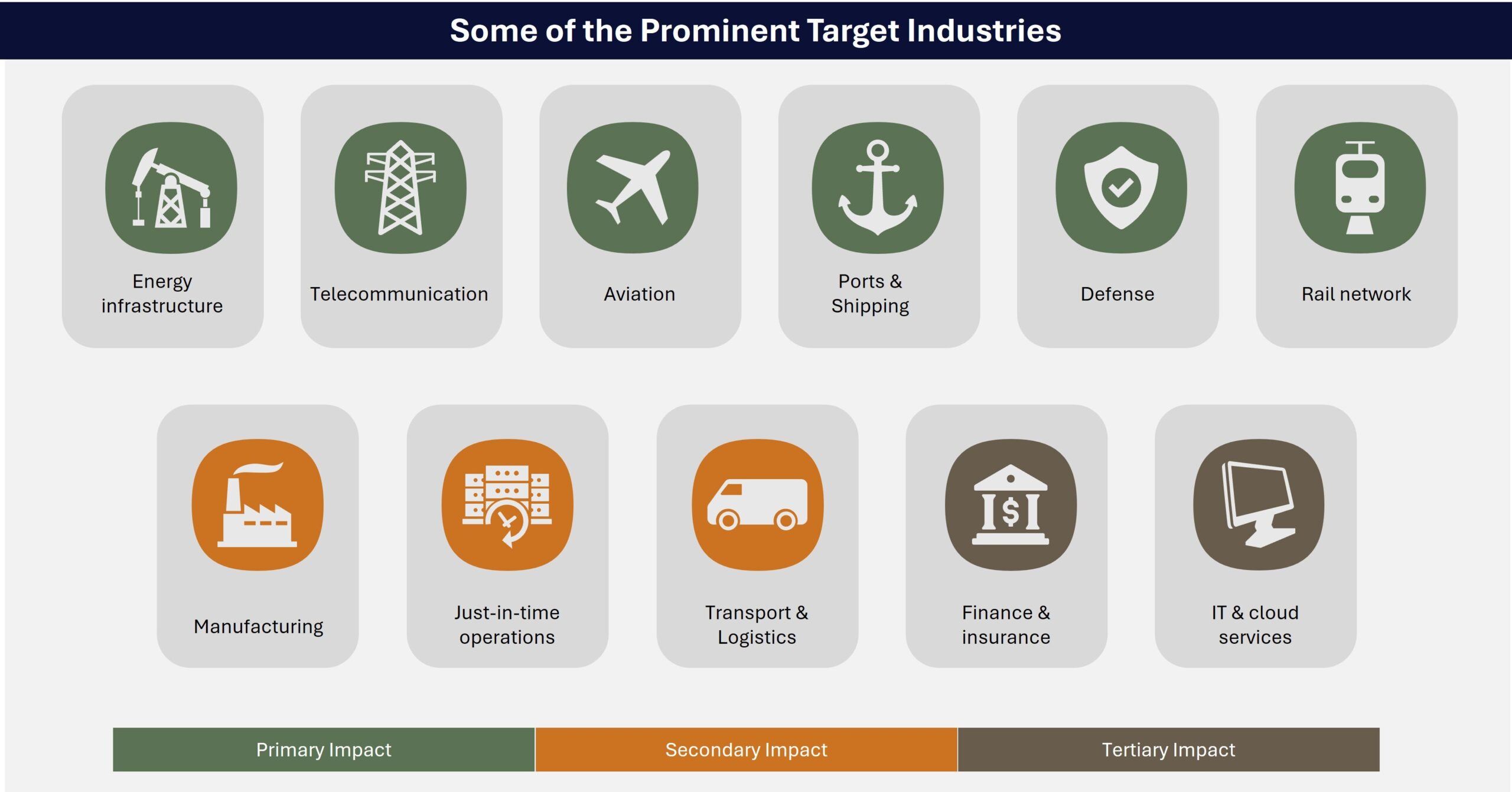
Highly interconnected physical and digital systems, along with geographically dispersed assets, increase threat exposure for transportation, telecommunication, and energy networks, as well as all the sectors that depend on them.
-
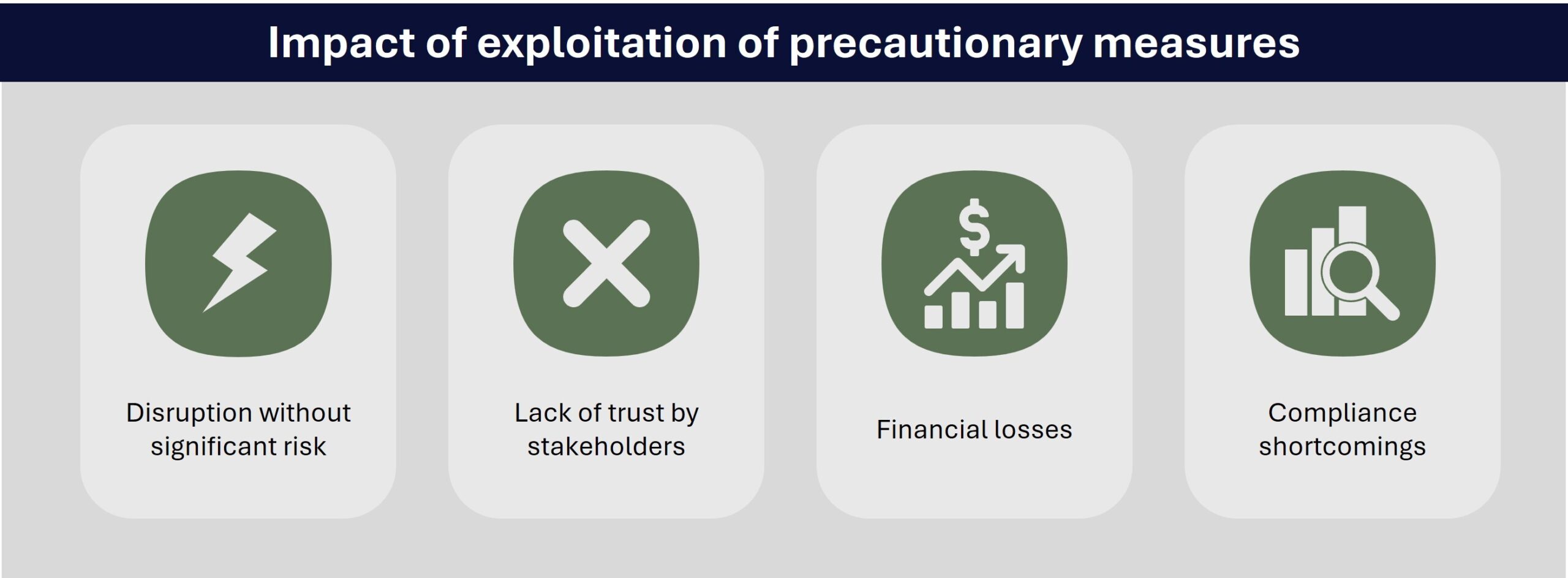
In addition to exploiting these weak points to cause disruption, perpetrators exploit precaution-driven safety protocols to trigger operational shutdowns through minor incidents, eroding compliance and trust.
-
For businesses, these repeated interferences are creating structural operational and financial pressures. Infrastructure disruptions result in delays, rerouting costs, inspection backlogs, and compliance burden across supply chains.
-
Consult intel@max-security.com for custom vulnerability mapping of physical chokepoints within supply corridors to identify low-cost disruption entry points. Businesses should strengthen perimeter controls, contractors and vendor vetting, and access management at substations, ports, data hubs, energy terminals and logistical chokepoints.
Introduction
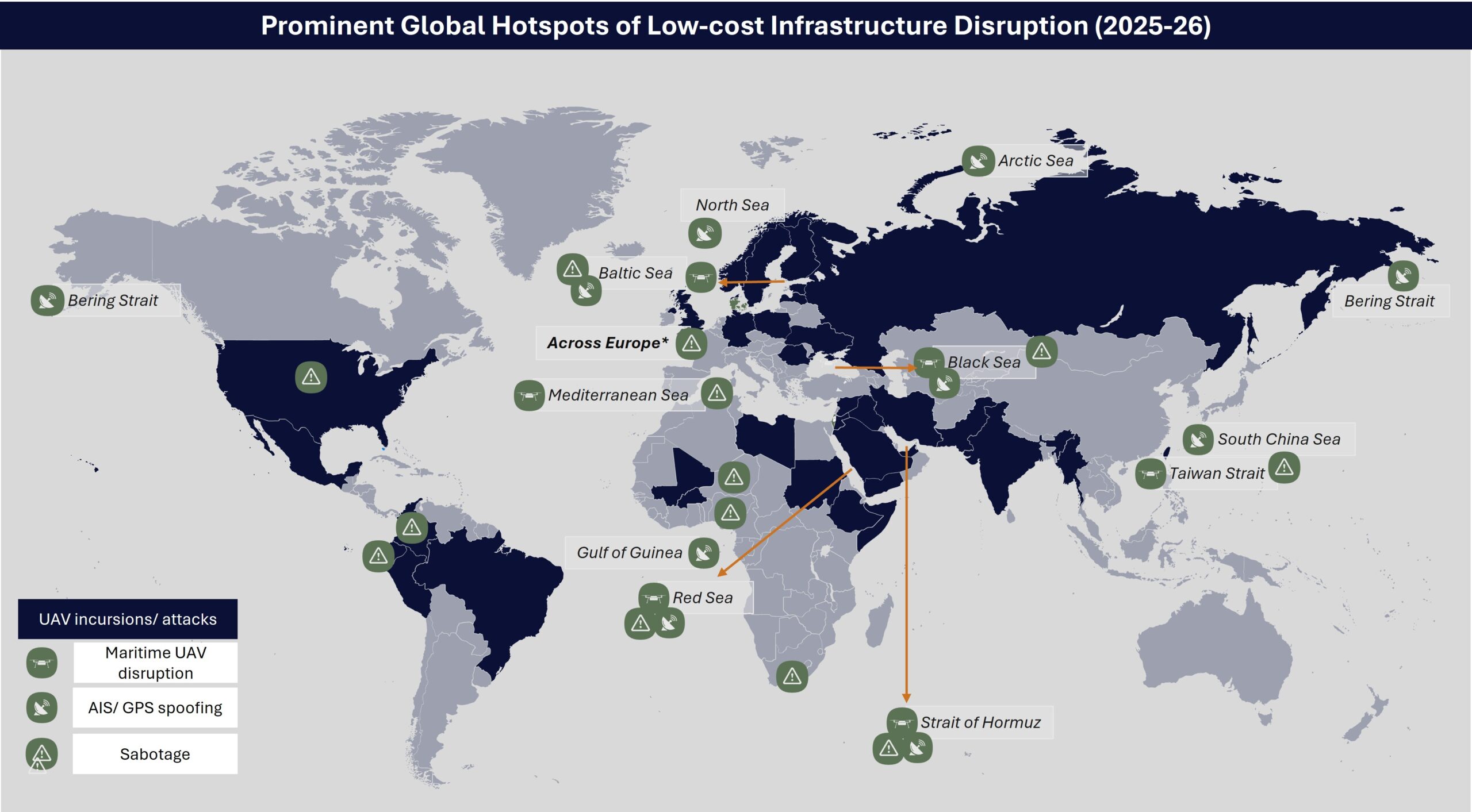
Critical infrastructure is facing elevated risk from the growing use of low-cost, low-technology, but high-impact disruption tactics deployed by states, state-backed proxies, criminal networks, and ideological activist groups. These methods require limited resources, yet most certainly impose disproportionate operational, psychological, and economic consequences by exploiting systemic vulnerabilities, rather than relying on large-scale physical destruction. Since 2024, for instance, multiple Unmanned Aerial Vehicles (UAVs) flybys across several European airports in cities like Amsterdam, Copenhagen, and Munich, and other countries like the US, Brazil, and Vietnam resulted in multi-million euros losses through airport closures, flight groundings, rerouting, crew overtime, passenger compensation, and fuel burn. This incident demonstrates how minimal input can generate operational disruption, and security responses, without even materially damaging infrastructure.
This risk is becoming structurally embedded due to inconsistencies across systems and networks as some critical infrastructure, both physical and cyber, has become aged and outdated, while other parts have been modernized. In some cases, even the modernization of systems and networks is uneven. Indeed, the mixing of new digital systems with old physical infrastructure can cause weaknesses in itself. This transnational expansion of physical and digital interfaces increases exploitable touchpoints across multiple sectors, such as energy, transport, and industrial networks.
Simultaneously, efficiency-driven and time-sensitive supply chains with limited redundancy allow localized interference like sabotage, arson, cyber intrusion, or hybrid tactics to cascade into broader operational disruption. These vulnerabilities present comparatively ‘easy wins’ for perpetrators, where minimal efforts can trigger precautionary shutdowns, delays, or costly inspections across interconnected systems. Geopolitical fragmentation further incentivizes the use of deniable and “below-threshold” tactics as instruments of economic competition and strategic signaling. The European Union’s 2026 security outlook highlights physical sabotage and arson among the most prominent risks facing infrastructure operators, reflecting growing concern among senior officials. Increasingly, low-cost disruptions are evolving from episodic security incidents into a persistent feature of the business environment, with sustained implications for business continuity and supply chain stability.
Evolving tactics are lowering barriers to infrastructure disruption, increasing vulnerabilities to business continuity
The operational manifestation of this shift is the expanding toolkit of low-cost disruption methods capable of interfering directly with critical infrastructure. Increasingly, actors deploy commercially available UAVs, improvised incendiary devices, and basic sabotage techniques to target logistical bottlenecks. For example, in 2025, UAVs allegedly operated by Iran-backed militias ignited fire at a natural gas facility in Northern Iraq, suspending production for months and contributing to electricity shortages in the region, while in 2024, Tesla’s Berlin factory’s operations were disrupted after far-left environmentalists set fire to remote electricity pylons in a forested area. Because these nodes function as transit and distribution chokepoints, even limited interference can disrupt flows of goods, data, or energy, generating ripple effects across downstream industries and supply chains. As a result, disruption increasingly focuses on operational continuity rather than physical destruction, enabling perpetrators to generate geopolitical signaling, political destabilization, economic pressure, or financial gain, while avoiding the risks associated with large-scale or deadly attacks.
Among these tools utilized for low-cost, high-impact attacks, the use of unmanned and other low-cost aerial systems have expanded significantly due to their affordability, accessibility, and operational simplicity. Commercial unmanned vehicles, remote-controlled devices, and modified small boats equipped with cameras are increasingly deployed to conduct surveillance, shadow or obstruct legitimate maritime and aviation traffic, and carry out limited strikes against energy assets, transport hubs, and industrial facilities. Actors have also adopted improvised airborne or floating objects, including weather balloons, and laser devices to disrupt logistics and transportation schedules or trigger precautionary responses near sensitive facilities. In late 2025, for instance, Lithuania declared a state of emergency after receiving numerous air balloons carrying contraband cigarettes from Belarus, triggering airspace monitoring, airport downtimes, and military mobilization.
State proxies and non-state actors are increasingly using commercially available technologies requiring minimal technical expertise or logistical preparation to approach restricted infrastructure and conduct interference operations at relative ease. For example, laser illumination incidents targeting commercial aircraft have increased significantly in recent years, averaging over 30 incidents per day in the US in 2025 and posing risks like pilot distraction, visual impairment, and unsafe flight operations. Small ‘quadcopter’ UAV devices have also been used for short-range clandestine transportation activities, such as smuggling across borders or into restricted areas, like prisons, as reported in the UK in 2025-26, as well as Mexico, France, India, the US, Jordan, Morocco, Israel, Brazil, and Spain. Even when such devices carry minimal payload or remain unarmed, sightings near critical areas like airports or industrial sites trigger inspection drills, precautionary shutdown, and security mobilization, producing disproportionate operational disruption relative to the cost of deployment.
FORECAST: These tactics are likely to proliferate because they exploit structural asymmetry between attackers and defenders. Effective mitigation requires costly technology installations, expanded surveillance coverage, and coordinated regulatory enforcement, all of which remain unevenly deployed across jurisdictions and systems. At the same time, attribution is often technically and legally difficult when incidents involve commercially available platforms that can be easily modified or remotely operated. Despite their relatively simple execution, interference targeting highly visible systems generates immediate operational consequences. Disruptions to both the businesses directly and to the customers ensure widespread public attention, making such methods attractive for actors seeking rapid impact.
Routine maritime and aviation systems themselves are increasingly manipulated to induce similar operational impediments. States proxies, traffickers, and illicit businesses, including smuggling networks operating along illegal migration routes, use signal interference such as GPS/GNSS jamming or spoofing, vessel transponder manipulation, and AIS misreporting to obscure vessel movement and evade regulatory authorities. Commercially available GPS spoofers and improvised software-defined radio (SDR) jammers can reportedly be obtained at rates between 100 and 1,000 dollars through both commercial and illicit marketplaces, lowering barriers for a wider range of actors.
As navigation and traffic management systems have become more technologically integrated, relying on satellite positioning, automated routing, and interconnected monitoring platforms, the number of potential interference points have expanded. By increasing the range of exploitable vulnerabilities, this has complicated traffic coordination and reduced navigational reliability for the shipping and aviation industry, increasing the likelihood of routing errors, accidents, or groundings. In maritime environments in particular, such incidents have increased both in scale and scope, jamming hubs increasing from three to ten globally within 2025, and impacted vessels rising from a few hundred to over 13,000. These incidents cause screening fatigue, prompt fake port calls, and often compel authorities to divert patrols, and search-and-rescue resources, while temporarily restricting commercial traffic across affected corridors.
FORECAST: As reliance on satellite navigation and automated routing systems continues to expand, interference with positioning signals will produce broader operational consequences across aviation and maritime systems. Persistent spoofing and jamming incidents will compel regulatory authorities to increase verification procedures and corridor restrictions to ensure navigational safety. Multilateral bodies overseeing telecommunications, maritime, and aviation standards have already called for increased international coordination to track and mitigate such threats, signaling a shift towards stricter compliance expectations. Operators are also adjusting routes using spoofing risk maps, which often increase transit time by 10-20 percent. These measures will introduce additional monitoring, reporting, and verification requirements, increasing compliance burdens while complicating scheduling reliability across affected routes.

Beyond signal manipulation, maritime infrastructure also remains vulnerable to low-cost physical interference. Subsea communication cables and offshore energy infrastructure have been damaged through deliberate or negligent anchor dragging and trawling activities capable of severing critical data links and interrupting telecommunications across regions. Since 2024, such incidents have been reported in the Red Sea, Black Sea, Baltic Sea, the South China Sea and Taiwan strait, allegedly attributed to Houthis, Chinese and Russian operations, respectively, which impaired cloud-dependent business operations globally. Although governments have sought to expand monitoring and deterrence mechanisms around sensitive maritime infrastructure, protecting widely dispersed networks remains difficult. For example, despite the deployment of a multinational monitoring initiative in the Baltic Sea in January 2025 to deter cable damage from anchor dragging, additional incidents have been reported throughout 2025, underscoring the challenges of comprehensively securing subsea infrastructure.
On a smaller-scale, states like Russia and Iran, criminal networks, and ideologically motivated protest groups increasingly recruit individuals through encrypted platforms like Telegram, to conduct low-skill attacks like arson, vandalism, reconnaissance, and infrastructure tampering, targeting critical infrastructure. Recruit profiles often include migrants, underage individuals, or those with previous criminal records who can be incentivized through modest payments and compartmentalized tasks, enabling operational deniability for organizers while generating political signaling or local disruptions. The growing availability of open-source data on infrastructure locations and operational criticality, combined with sabotage playbooks and campaign models through encrypted online communities, is lowering barriers for participation in such activities. As a result, smaller networks and loosely organized actors are also adopting similar tactics because they offer relatively low execution risks but potentially high public visibility and economic impact. These perpetrators often time deploy such actions around major political events, international gatherings, or periods of tightened security presence, when even minor incidents can attract outsized media attention and operational response, such as sabotage-induced rail disruptions during the openings of the Paris 2024 and Milan 2026 Olympics.
These actors frequently target geographically expansive infrastructure systems such as energy transmission networks, rail corridors, and logistics hubs, whose dispersed operational nodes create areas of limited surveillance and uneven security coverage. As these systems function as upstream operational chokepoints, disruptions rarely remain confined to the immediate site of interference. Manufacturing sectors reliant on just-in-time delivery models like automotives, pharmaceuticals, and electronics production are particularly exposed to delays when ports, rail hubs, or energy supplies are interrupted, often triggering missed delivery deadlines, contractual penalties, and broader supply chain slowdowns. For many actors, targeting such infrastructure also represents a more feasible strategy than attempting to strike well-protected corporate or industrial facilities directly. As a result, attackers increasingly seek indirect disruptions by interfering with enabling infrastructure on which businesses depend. As mentioned above, in March 2024, an activist group claimed an arson attack on an electricity pylon near Tesla gigafactory halted factory production for days, reportedly costing the company hundreds of millions of euros.
FORECAST: Interference targeting transport, energy, and communication infrastructure is likely to intensify as geopolitical fragmentation, ideological polarization, and other pressures increase incentives for asymmetric disruption. State actors will continue leveraging hybrid tactics capable of generating economic disturbance while maintaining plausible deniability, particularly in strategically sensitive maritime corridors and logistics hubs like Black Sea and Baltic Sea. Non-state actors will also leverage the effectiveness of these low-cost disruptions to advance political objectives, or facilitate illicit trade, amid tightening traditional security measures globally.
Overtime, repeated low-level interference across essential infrastructure will reshape how businesses manage operational risk. Companies dependent on vulnerable logistics corridors may be forced to incorporate greater redundancy into transport routes, expand contingency planning, and maintain higher inventory buffers to absorb delays. As incidents accumulate, insurers and regulators are also bound to tighten infrastructure protection and reporting expectations, increasing compliance burden and operational costs for both infrastructure operators responsible for system security and the firms reliant on these networks for logistics, energy supply, and communications.
Perpetrators exploit known responses, defensive measures to maximize disruptions
In addition to direct physical interference and cyber intrusion, disruption strategies are increasingly shifting toward the exploitation of institutional safety frameworks and automated responses. Critical infrastructure environments operate under precaution-driven doctrine that mandates work suspension, thorough inspection, or even evacuation when credible safety or security risks are identified. While these protocols are foundational to risk mitigation, their low tolerance for uncertainty creates structural vulnerabilities. Adversaries and threat actors are manipulating or fabricating risk signals or overloading systems at limited costs, triggering operational shutdown and regulatory escalations without directly damaging infrastructure assets.
Hoax threats represent one of the most direct manifestations of this tactic. Because infrastructure operators are required to respond to credible threat signals under established safety and security protocols, even anonymous warnings or safety complaints must trigger precautionary procedures. The anonymity of such messages complicates attribution and verification, compelling authorities to treat them as potentially credible until proven otherwise. Although such threats often prove unfounded, the mandated response still produces immediate business continuity challenges. For instance, in 2024 and 2025, several bomb threats to Indian airports and Indian airlines globally led to extended groundings for inspection, emergency landing, and fighter jet escorts. Cargo and passenger movement were exposed to rescheduling and delays across the impacted routes and airports, leading to heightened operational costs, and security scrutiny at impacted logistical hubs. In addition to incurring financial costs, passenger inconvenience and repeated security threats also caused reputational harm to the Indian aviation industry internationally, all from the low-tech, low-cost tactic of placing false threats.
Disinformation campaigns amplify this vulnerability by accelerating the spread of unverified information or allegations before verification processes can occur. Claims regarding operational failure or regulatory violations are rapidly circulated across social media platforms at low-cost, attracting public attention and promoting scrutiny from regulators, investors, and customers. The resulting information pressure forces companies and oversight bodies to demonstrate tangible responsiveness, such as operational adjustments or enhanced monitoring, to reassure stakeholders. These responses can generate measurable disruptions to routine operations even when the underlying claims remain unsubstantiated. In 2025, for instance, a fabricated incident report resembling an official aviation investigation circulated widely online, alleging pilot responsibility for a crash involving an Indian airline. Although later identified as fraudulent, the narrative triggered heightened scrutiny and additional safety checks that contributed to 15 percent of flight cancellations in the next three months. This incident illustrates how rapidly circulating safety narratives can generate sustained operational disruption for infrastructure-dependent businesses.
A related vulnerability emerges from the growing reliance of critical infrastructure on automated digital monitoring systems that guide real-time operational decisions. Because these systems depend on continued data flows, manipulation of operational inputs or poisoning of analytical models can distort system readings and undermine confidence in the signals used to manage infrastructure assets. As digital information platforms increasingly integrate with operational control environments, the boundary between data monitoring and physical system response is becoming progressively blurred, expanding the range of entry points for malaise data to disrupt operations. In safety-critical environments where precautionary doctrines prioritize risk avoidance, such uncertainties trigger conservative responses, including suspension of automated functions or temporary shutdowns while anomalies are investigated.
In active conflict environments such as Ukraine, Israel, and Jordan, cyber operations targeting critical infrastructure through operational data manipulation, disruption of monitoring systems, and interference with industrial control systems have caused significant operational instability and outrage. Similar incidents are not being reported in other regions, such as the US, where operational data and automation systems of water and wastewater systems, as well as energy facilities, have been targeted, causing financial losses and service interference. Scenario analysis highlights how manipulated operational data can generate false system alerts or safety anomalies in digitally integrated technologies, suspending work for a few hours to days. In San Francisco in October 2025, some 50 autonomously operated taxis were ordered to a dead-end street, trapping the vehicles and disrupting the affected app’s services in the region. While ostensibly a prank, the incident highlights the easy manipulation of such automated systems and responses to disrupt key services. As with the war in Ukraine inspiring many actors to rethink how they can use low-cost UAVs, these kinds of incidents can be inspirations for clandestine acts in the future.
FORECAST: With increasing integration of automated systems, data-driven monitoring tools, and Artificial Intelligence (AI) models in infrastructure management, industry assessments increasingly flag rising exposure to operational disruptions. For example, growing uncertainty over the integrity of operational data will slow decision-making as operators introduce additional verification procedures before authorizing routine activity. Heightened scrutiny will also extend to third-party vendors responsible for system maintenance, software integration, and data management, lengthening onboarding timelines and compliance reviews across infrastructure networks. Over time, this environment will favor operators capable of demonstrating verifiable system integrity and resilient monitoring architectures, while smaller vendors and service providers may face heightened barriers to participation in infrastructure supply chains.
Conclusion
Low-cost, high-impact disruption has become a normalized instrument of geopolitical competition, ideological contestation, and opportunistic criminal activity. Rather than seeking decisive destruction, perpetrators are increasingly exploiting dispersed, interconnected infrastructure systems and precaution-led operating models to generate recurring economic frictions. Accelerating technological diffusion and deepening geopolitical fragmentation will continue to reduce thresholds for disruption. Businesses operating across global logistics corridors, energy networks, and digital communication systems, therefore, face sustained exposure to low-intensity but operationally consequential disruptions. Companies operating in contested regions or strategic chokepoints face sustained pressure to invest in layered monitoring, redundancy planning, vendor diversification, and regulatory coordination. Over time, these pressures are likely to embed higher operational buffers and security costs into infrastructure management, reshaping how firms price risk, allocate capital, and plan supply chain resilience.
Recommendations
-
Consult intel@max-security.com for custom threat monitoring services to ensure early identification of geopolitical triggers and other challenges, along with assistance in exposure assessments and other safety and security needs.
Operational resilience
-
Consult intel@max-security.com for custom vulnerability mapping of physical chokepoints within supply corridors to identify low-cost disruption entry points. Following, businesses should strengthen perimeter controls, contractors and vendor vetting, and access management at substations, ports, data hubs, energy terminals and logistical chokepoints.
-
Organizations should deploy layered detection systems combining radar, radio frequency signal monitoring, optical tracking, and anomaly analytics to identify unauthorized aerial or surface activity near critical sites.
-
Businesses’ redundancy planning should extend to backup power, alternative routing, and spare component availability to prevent single-point failures from translating into prolonged disruptions.
-
Businesses, particularly in Europe, should seek assistance in monitoring recruitment patterns on encrypted platforms, and regional protest escalation cycles to ensure early warnings for operational threats.
Supply chain vulnerabilities
-
Businesses should diversify sourcing arrangements, reassess just-in-time dependencies, and build inventory buffers for critical inputs where feasible, particularly for businesses where supply chains are closely associated to high-risk regions.
-
Businesses should assess insurance coverage and contractual exposure related to unmanned systems triggered operational suspensions.
Cyber threats & data integrity
-
Businesses are advised to strengthen access controls and ensure clear network segmentation between operational technology (OT), information technology (IT), and administrative systems to reduce the risk of lateral movement during cyber intrusion.
-
Organizations should conduct regular cyber risk assessments and penetration testing across both operational and corporate environments, including third-party and remote access points, to identify and remediate exploitable vulnerabilities.
-
It is advised to develop and routinely drill incident response procedures for ransomware, location spoofing, and data breaches to ensure rapid isolation of affected networks, preserve evidentiary data, and continuity of critical operations.
-
Businesses should integrate information integrity in the enterprise risk framework and designate a cross-functional unit across operations, physical and information security, compliance, and communications to build clear inter-departmental understanding of the risks and ensure swift decision-making in crisis.