MAX INTELLIGENCE
Protective Intelligence
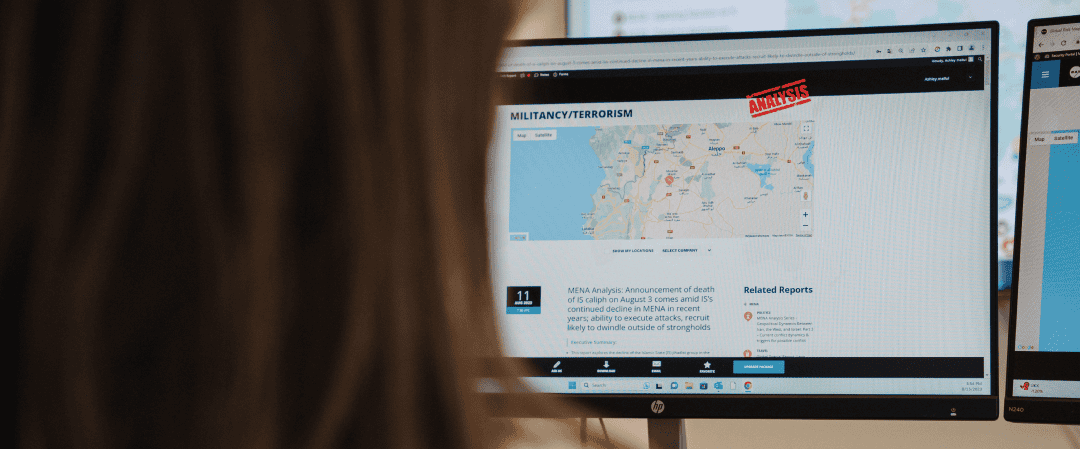
Defend Your Digital Presence with Advanced Intelligence
Identify and mitigate threats to your leadership, facilities, brand, and reputation. Our holistic approach to protective intelligence combines online investigations with continuous monitoring of open sources and hidden networks, giving you the intelligence to act confidently and stay protected on all fronts.
Exposure Assessments
A detailed review and in-depth analysis of your digital footprint reveals publicly accessible information that could pose a risk. We identify sensitive details, personal data, and exploitable content, providing a clear view of vulnerabilities so you can take steps to reduce exposure.
Continuous Threat Monitoring
Our ongoing surveillance keeps watch over open sources, social media, and hidden networks to detect threats that could impact your brand, executives, or operations. From negative sentiment to direct dangers, we deliver customized intelligence reports to help you proactively address risks.
Targeted Online Investigations
Combining automated tools and manual expertise, we investigate and uncover the sources behind threatening emails, negative campaigns, and other harmful activities. Our findings provide actionable insights to enhance both your online and physical security strategies.
Why Choose MAX Protective Intelligence?
-
Proactive Risk Management: Identify risks before they escalate.
-
Comprehensive Security: Protect your organization from digital and physical risks.
-
Customized Insights: Receive tailored intelligence that meets your unique challenges.
Complete the Picture with Travel Intelligence
For individuals exposed to elevated risks during travel, protective intelligence doesn’t end online. Our itinerary-based monitoring service applies the same threat-driven methodology to physical movement, combining real-time alerts, pre-trip assessments, and emergency response protocols to safeguard travelers at every stage of their journey.
Frequently Asked Questions
How does protective intelligence differ from traditional security measures?
Protective intelligence is proactive, focusing on identifying and mitigating threats before they escalate, whereas traditional security often reacts to incidents after they occur. By analyzing data from various sources and monitoring online activities, protective intelligence offers a forward-looking approach that enhances overall security.
What are the most common vulnerabilities found in online exposure assessments?
Online exposure assessments often reveal vulnerabilities such as exposed personal information, unsecured digital assets, and outdated security practices. Understanding these common risks allows organizations to take specific actions to safeguard their digital presence.
How does protective intelligence integrate with other security measures?
Protective intelligence works best when integrated with broader security protocols, including physical security measures, cybersecurity defenses, and crisis management plans. This integration provides a unified approach that enhances overall security by ensuring that digital and physical threats are managed cohesively.
What role does human expertise play in online investigations?
While automated tools are essential for handling large volumes of data, human expertise is crucial in interpreting complex patterns, identifying subtle threats, and making informed decisions. Experienced analysts can provide insights that machines might miss, ensuring a more thorough investigation.
What should organizations look for when choosing a protective intelligence partner?
Key factors to consider include the provider’s experience in handling similar threats, the use of advanced technologies and methodologies, the ability to deliver tailored and actionable insights, and their track record in helping clients prevent or mitigate security incidents effectively.
What are the latest trends in digital threats organizations should be aware of?
The threat landscape is constantly evolving, with trends like deepfake technology, AI-driven cyber attacks, and coordinated misinformation campaigns becoming more prevalent. Staying informed on these trends through protective intelligence helps organizations adapt their strategies and maintain resilience against new types of threats.
IT’S A TOUGH WORLD