MAX PROTECTION
Physical Security Risk Assessments
Identify Vulnerabilities to Strengthen Your Defenses
Fortify your organization against today’s relentless threats with MAX Security’s Physical Security Risk Assessments. Using advanced intelligence gathering and proven operational strategies, our advisory service offers a comprehensive approach to safeguarding your assets.
Comprehensive Security Assessments
Overlooking a single vulnerability can have serious consequences. Gain critical insights into your security environment through a detailed assessment of technology, personnel, and existing practices. Our evaluations identify vulnerabilities and provide a clear foundation for developing an effective risk management strategy.
Physical Security Audits
As an additional layer of protection, our audits examine the integrity of your security systems, from access to CCTV surveillance, to pinpoint weaknesses and recommend specific improvements, such as enhancing perimeter defenses and refining personnel deployment.
Industries Covered
MAX has extensive experience in critical sectors like mining, oil, gas, and healthcare. Our Risk Assessment service leverages this expertise to deliver specialized solutions that address the unique challenges of your industry. From managing security for large events to protecting sensitive sites, we address potential threats with focused, practical solutions.
Need a Physical Security Risk Assessment?
Request a Consultation
Frequently Asked Questions
How often should a physical security audit be conducted?
It’s recommended to conduct a physical security audit at least annually, or whenever significant changes occur in your organization’s operations, technology, or personnel. Regular audits help ensure that your security measures remain effective and adapt to evolving threats.
What specific threats does MAX Security’s risk assessment service address?
Our risk assessment service is designed to identify and mitigate a wide range of threats, including unauthorized access, surveillance gaps, insider threats, and vulnerabilities in emergency response plans. By addressing these threats, we help you build a resilient security posture tailored to your industry.
Can MAX Security’s services be customized for smaller businesses?
Absolutely. While we specialize in serving critical industries like mining, oil, gas, and healthcare, our risk assessment and physical security audit services can be tailored to meet the specific needs of businesses of any size. We provide scalable solutions to ensure comprehensive protection, no matter the scope of your operations.
What is the process for implementing the recommendations from a physical security audit?
After conducting a physical security audit, we provide a detailed report outlining our findings and recommendations. Our team will work closely with you to prioritize these recommendations and develop an actionable plan for implementation, ensuring that your security enhancements are effective and aligned with your organization’s goals.
How does MAX Security stay updated on the latest threats and security trends?
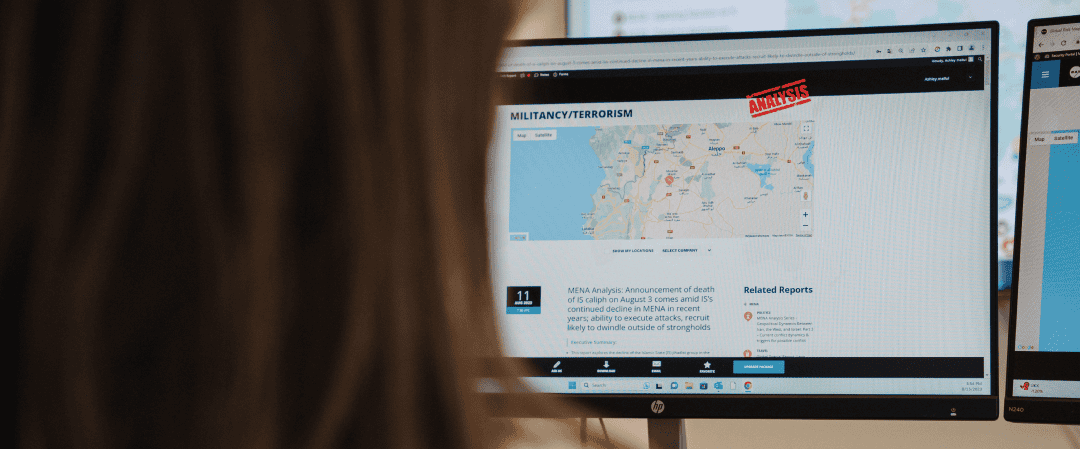
MAX Security continuously monitors global security trends and threats through our elite intelligence network and operational expertise. We regularly update our methodologies and recommendations to reflect the latest developments in the security landscape, ensuring that our clients are always protected against emerging risks.
IT’S A TOUGH WORLD